The Evolution of Identity Management in Tamil Nadu
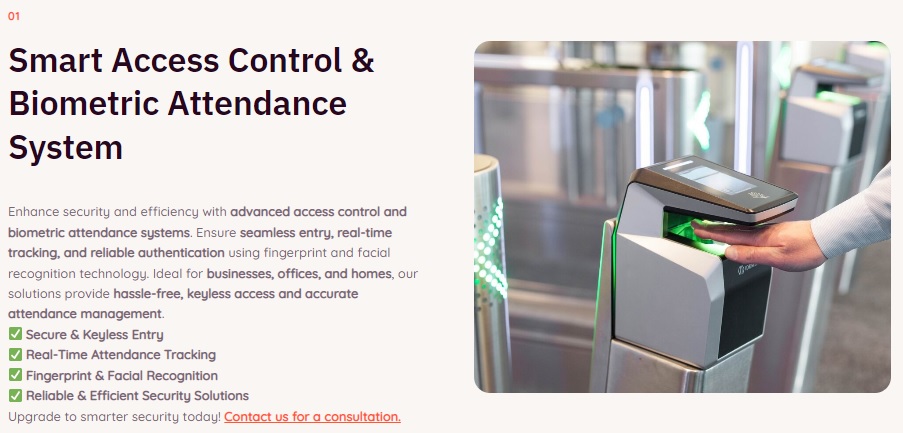
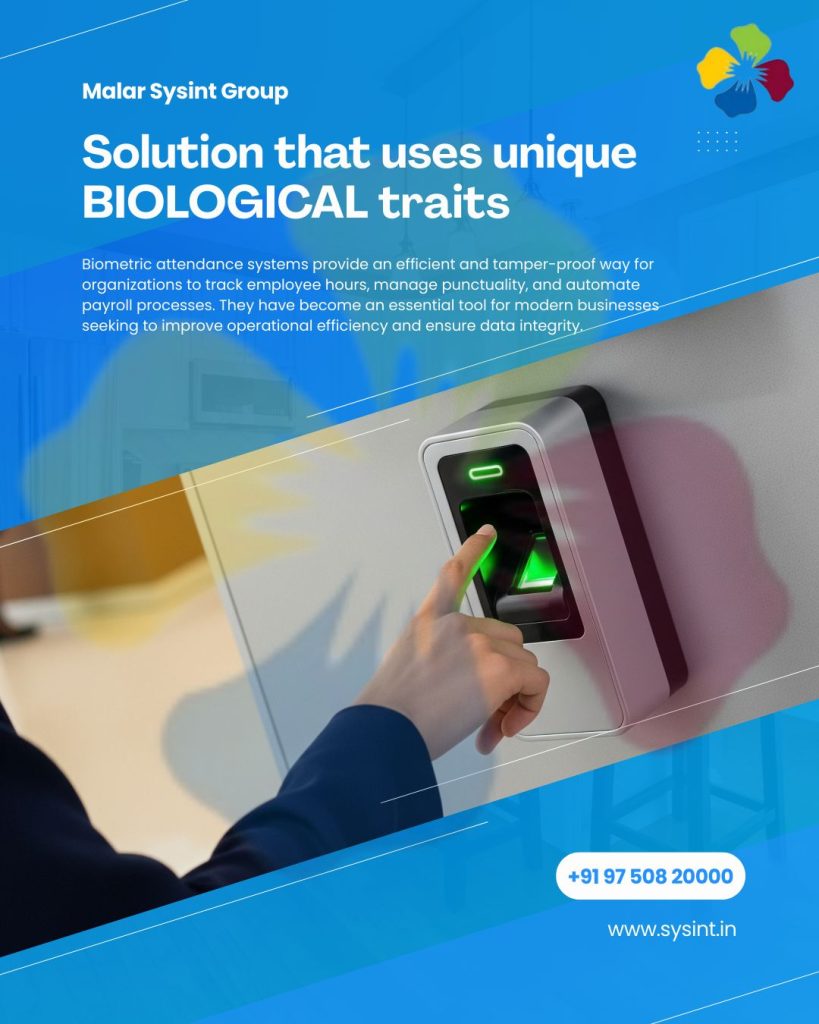
In the industrial corridors of Tamil Nadu, the demand for high-end biometric systems Namakkal has undergone a paradigm shift. Business owners are no longer looking for a simple “digital register.” They are demanding a Unified Shield: a single, tamper-proof biometric nervous system that automates workforce logic, protects high-value data centers, and plugs profit leaks in canteen operations.

At Malar Sysint Group, we have built our reputation on a non-negotiable standard: Zero Compromise. In our 15-year history, we have established a strict protocol: We have never installed a “basic” or entry-level device. We strictly deploy enterprise-grade hardware, specifically recommending the eSSL x990, uFace302, and the AI Face Mars series. In a high-stakes industrial environment, the “cheap” option is the most expensive mistake a business can make. This guide explores the technical depth of our integrations and why the “Malar Standard” is the benchmark for the region.
Chapter 1: The Engineering of Presence – Beyond Simple Attendance
Attendance tracking is the heartbeat of any organization. However, a heartbeat is useless if the data is inaccurate. When you manage a workforce across three shifts, “lost time” and “buddy punching” are your biggest hidden taxes.
1.1 The eSSL x990: The Industrial Workhorse
For environments where reliability is paramount, we recommend the eSSL x990. This isn’t just a fingerprint reader; it is a high-capacity transaction engine.
- Optical Precision: Equipped with a 500 DPI optical sensor, the x990 reads prints that other machines miss—oily, dusty, or worn-down fingers typical of Namakkal’s transport and manufacturing sectors.
- Storage Capabilities: With a capacity for 3,000 fingerprints and 100,000 logs, it handles large-scale labor forces without a glitch.
- Network Stability: Built-in TCP/IP and optional Wi-Fi/GPRS ensure that attendance data is pushed to the server in real-time, even during local network fluctuations.
1.2 Intelligent Shift & Night Shift Logic
Most software fails at the “Midnight Crossover.” If a worker clocks in at 10:00 PM Monday and out at 6:00 AM Tuesday, budget systems often record two separate, broken shifts.
- The Malar Algorithm: Our custom-configured software recognizes shifts that span across two calendar days. It automatically attributes the entire duration to the correct working day.
- Night Shift Premiums: The system automatically identifies hours worked during the night window (e.g., 10 PM to 6 AM). It calculates night shift allowances instantly, removing hours of manual work from your accounts department and ensuring your staff is paid accurately.
Chapter 2: High-Stakes Access Control – Securing the Brain Center
A door is only as secure as the logic behind the lock. For server rooms and MD cabins, Malar Sysint implements a Two-Way Vault Protocol.
2.1 The uFace302: Multi-Modal Mastery
For sensitive executive areas, we deploy the uFace302. This device offers a sophisticated blend of Facial Recognition and Fingerprint scanning.
- MFA (Multi-Factor Authentication): For high-security zones, we mandate two forms of ID. You might use a Face Scan + Fingerprint or Face + PIN. This ensures that even if a credential (like a card) is stolen, the physical presence of the authorized person is mandatory.
- Infrared Integration: The uFace302 uses high-resolution infrared night vision cameras. This allows for near-instant recognition even in pitch-black server rooms or dimly lit corridors.
2.2 Server Room Sovereignty: Entry & Exit Tracking
We treat the server room as a two-way secure zone. By installing separate devices for entry and exit, we create a minute-by-minute audit trail.
- The Logic: We log not just who entered, but exactly when they left. This prevents “ghost sessions” where a door might have been left ajar or an unauthorized person stayed inside after an authorized entry. This is the difference between “closing a door” and “securing a zone.”
Chapter 3: AI Face Mars – The Future of Touchless Security
In 2026, hygiene and speed are non-negotiable. The AI Face Mars series represents the pinnacle of AI-driven biometric engineering.
3.1 Proactive Facial Recognition
Unlike older models that require you to stand still, the Mars series uses Visible Light Facial Recognition.
- 3-Meter Recognition: It identifies authorized personnel from up to 3 meters away while they are walking. This eliminates “gate-out bottlenecks” during shift changes.
- Deep Learning Algorithms: The system is programmed to recognize faces even with masks, glasses, or varying lighting conditions.
- Anti-Spoofing Technology: The AI algorithm can distinguish between a real human face and a high-resolution photo or 3D mask. Your security cannot be bypassed by a smartphone screen showing a photo of an employee.
Chapter 4: The Digital Canteen – Automating the Mess
The staff canteen is often a company’s biggest “leakage” point. Manual coupons are easily duplicated, leading to food waste and financial loss.
4.1 The Touchless Token Workflow
We replace messy paper coupons with a seamless Biometric Token System.
- Verification: The employee scans their face or finger at the canteen kiosk.
- Entitlement Check: The system verifies if the employee has already eaten or if they are authorized for that specific meal (Breakfast/Lunch/Dinner).
- Instant Token: A high-speed thermal printer issues a token only if the employee has already punched “IN” for their shift.
- Zero Waste: By knowing the exact headcount by 10 AM, your kitchen can cook the precise amount of food needed, reducing waste by up to 30%.
Chapter 5: The Smart Gym – 24/7 Unmanned Operations
For Namakkal’s modern fitness centers, membership integrity is the key to profit. Malar Sysint automates this entire cycle.
5.1 Automated Membership Enforcement
- The Expiry Trigger: When a gym membership expires in the software, the biometric gate (Turnstile or Flap Barrier) locks automatically.
- Reception Bridge: While the gate stays locked, an instant notification is triggered at the reception desk, allowing staff to handle renewals professionally.
- The Guest Bell Switch: For newcomers, we integrate a dedicated bell switch. This allows the reception to grant manual entry for guests or trials, ensuring the automated system doesn’t hinder sales opportunities.
Chapter 6: The “Gate-Out” Protocol – The Final Line of Defense
A common problem in large factories is “early leakage,” where workers leave their stations 20 minutes before the shift ends. To prevent this, we implement a Digital-to-Physical Exit Workflow.
6.1 The Physical-Digital Bridge
- Workstation Punch: The worker scans their biometric at the departmental exit terminal.
- The Exit Slip: A thermal slip is printed containing Employee ID, Exit Time, Reason for Exit, and Department.
- Security Record: This slip is handed to the security person at the main gate out. This creates a hard-copy record that ensures every person leaving the facility has a valid digital exit log, providing an extra layer of human verification for your industrial security.
Chapter 7: Data Sovereignty & Power Resilience
A security system is only as good as its uptime. In Namakkal, where power fluctuations are common, Malar Sysint standards are higher than the market average.
7.1 Database Redundancy & Sync
We follow a “Local-First, Cloud-Always” philosophy to ensure data integrity.
- Primary Storage: Data is initially stored at the device level, ensuring zero data loss during network outages.
- Automated Sync: At specific intervals (e.g., every 15 minutes), data is pushed to the central server.
- Client Choice: Based on your security policy, we host this server Locally (On-Premise) or in the Cloud (via eTimeTrack Lite Web) for remote management across multiple factory branches.
7.2 UPS-Backed Infrastructure
We do not believe in “power-dependent” security. Every device we install—from the x990 at the gate to the uFace302 at the MD room—is connected to a proper UPS power backup. This ensures that even during a total blackout, your locks remain active, and your attendance logs remain continuous.
Chapter 8: ERP & Payroll Integration
We bridge the gap between “Hardware” and “Human Resources.”
- eTimeTrack Lite: We offer industry-standard licensed software (Window or Web-based) for standard payroll needs.
- Customized ERP: If your organization requires deep integration with Tally, SAP, or a custom-built ERP, our engineers provide the API hooks and data-push protocols needed to automate your payroll 100%. This eliminates human error in salary processing.
Chapter 9: The “Malar Brand” Reputation – Why We Say No to Basic
The local market is flooded with “budget” biometric sellers. Malar Sysint Group stands apart because we are System Integrators, not “box-movers.”
9.1 The 4-Hour Response Guarantee
If your biometric gate at a spinning mill in Tiruchengode or Mohanur fails at 8:00 AM, you cannot wait for a technician from Chennai.
- The Malar Guarantee: We are based in Namakkal. We offer a 4-hour response window within a 50km radius. We keep your business moving while others are waiting for parts.
9.2 Our History of Quality
We stand strictly with the Malar brand reputation. Our past history shows we have never installed basic model devices. We believe that if a machine cannot withstand the 24/7 heat and dust of a Namakkal factory, it has no place in your business. By recommending only high-end eSSL and ZKTeco hardware, we ensure that your investment lasts for 5 to 7 years, rather than 5 to 7 months.
Chapter 10: Conclusion – An Asset, Not an Expense
In the world of industrial technology, Price is a one-time conversation; Performance is a daily reality. A cheap biometric system saves you money today but costs you lakhs in payroll fraud, hardware downtime, and security breaches tomorrow.
Investing in a Unified Shield from Malar Sysint Group is an investment in peace of mind. You focus on your production; we will focus on your protection. Whether you are in Rasipuram, Paramathi Velur, or the heart of Namakkal, Malar Sysint is your partner in technical excellence.
Ready for a Smarter, More Secure Facility? Stop managing your business with 2010 technology. Let the experts at Malar Sysint Group design your infrastructure.
Contact us to see why we are the leaders for biometric systems Namakkal industries trust. For the best biometric systems Namakkal has to offer, Malar Sysint Group is your trusted partner.
Contact Details:
- Phone: +91 97508 20000
- Email: info@sysint.in
- Address: #80, Ground Floor, State Bank Colony, Trichy Road, Namakkal – 637 001.
- Web: www.sysint.in